WPCD V 4.7.x has ZERO new features. Instead it is a release focused on bug-fixes, code improvement and, more importantly, a release that has been audited for security issues by a third party.
If you’re looking for information about new features, please check out the announcement from our last release – version 4.6.0 (or any of our many other releases.) Those were all chock-full of new features.
The Security Audit
We first sent WPCD out for a security audit in October 2020 so it was time for another, given the many features we’ve released between then and now.
This time around, our auditor only found 3 low priority issues which we have resolved in V 4.7.1
The first time around (last year October) there were:
- Zero critical issues
- One high priority issue
- Zero medium priority issues
- Five low priority issues and
- Three informational issues
This time there were:
- Zero critical issues
- Zero high priority issue
- Zero medium priority issues
- Three low priority issues and
- Zero informational issues
The much improved security profile is primarily a result of our improved development processes.
About The Process
We used the same firm from our last audit to conduct this one – WPScan – and worked with Ryan again.
Because they were already familiar with the plugin, things were a lot simpler this time around. We didn’t have to conduct training or go through multiple rounds of testing.
Instead, we just sent an email that said something to the effect of “hey, can you do this again?” An audit date was set and that was it. Seven days after the audit date we had the final report in our hands.
Issues Found
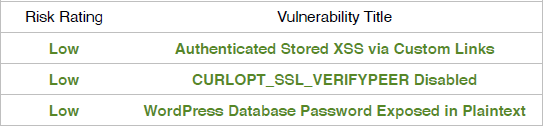
As mentioned earlier, three issues were found. These were:
All three issues have been resolved in the latest version of WPCD. None of them posed a significant threat – if you’re concerned you can read the unvarnished discussion and conclusions from the auditors (just request a copy of the audit report by opening a support ticket.)
Edit: We posted this article on our FB page and someone commented on it – they wondered why the “WordPress Database Password Exposed In Plaintext” was a low priority issue. We aren’t the ones that categorizes issues as “high, low, etc.”; the auditors are the ones that make that determination. In this case, the exposure was in logs that only the Admin has access to and the logs were routinely deleted. Hence, the low priority. Usually these things are encrypted or scrubbed automatically. If it was an exposure to the public it probably would have been categorized as a SEVERE issue instead. The headline made it more worrisome than it was but as with all things security related, context matters a lot!
Risk Ratings
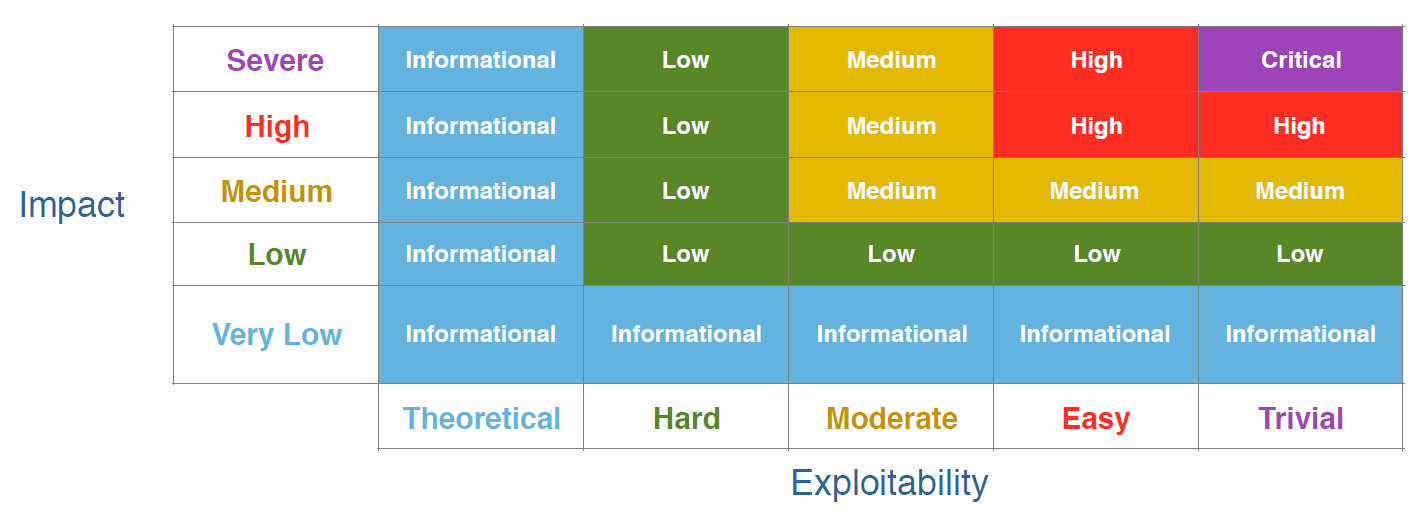
If you’re wondering how the risk ratings are calculated, here is the matrix that was used to assign them:
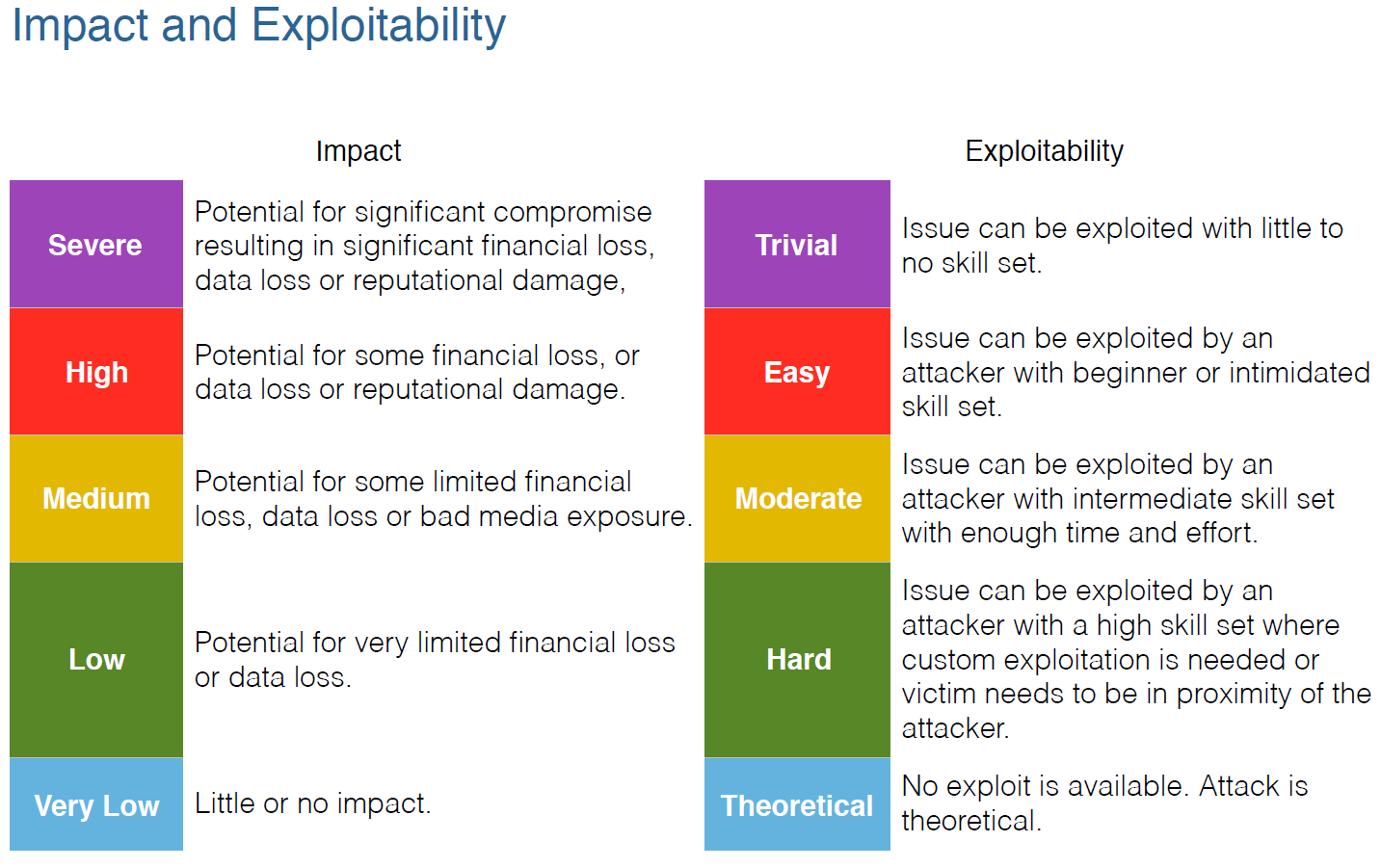
And here are the definitions of some of the elements used in the matrix:
Our Full Disclosure Policy
So, why are we making this information public? Because we believe in transparency. It’s already been proven that, in the long run, hiding security issues simply reduces trust and enables the bad actors.
Every time an issue is found, it just enhances the security profile of our product. We want security issues, if they exist, to be rooted out as fast as possible!
And by making the information public we hope that it gives you the confidence you need that we’re not going to be hiding anything from you!
As we said after the results of our first audit last year:
Any vendor that tells you that their product has no security issues is blowing smoke – the best they can tell you is that it has no security issues that THEY know about.
Our approach is to always assume that our code is insecure and write everything defensively.
No one gets this stuff right 100% of the time. No one! Every month you see security updates from the likes of Microsoft, Google, Apple etc. Why would comparative tiny software publishers like ourselves (and others) be immune? Assuming that we’re perfect in this area would just be burying our heads in the sand and, in the process, do a huge disservice to our customers.
Instead, you should take comfort in knowing that security is a top consideration for us and public audits like this one is just part of that.
Note: Any current customer can request a copy of the 3rd party audit report by opening a support ticket.
Additional WPCD 4.7 Changes
We mentioned earlier that this release does not include any new features. This is because we spent a lot of time on cleaning up the code so that it adheres to some of the more basic WordPress coding standards. We still have some work to do in this area but most of the obvious standards issues were resolved. The ones that are remaining would involve substantial changes to the codebase so we’re going to handle those at a much slower, more deliberate pace.
As with every release, we addressed a few bugs – for a full list please see the plugins’ readme.txt file for details or the history log at the bottom of the product page on our site.
Finally, we updated the PHPSecLib library to the latest version and added new functions and filters that add-ons can use. Some add-ons are already using these new developer focused changes and are required if you upgrade to WPCD 4.7.
Wrap Up
If you’re a reader who do not routinely read or encounter security-related articles, this disclosure might completely scare you. It all sounds really bad to the lay person. However, you should know that even the largest companies find issues whenever they do security audits – it’s a constant, on-going battle between the “whitehats” and “blackhats”. The key here is that companies are being proactive about security instead of sitting back and letting bad actors find and exploit them.
At this point for WPCD:
- The plugin has twice had PROFESSIONAL security researchers attempting to find as many holes as possible.
- The issues that were discovered have been fixed.
- The researchers only found three low priority issues. No critical issues, no medium level issues and no high priority issues were found. Which means that you have a level of confidence that our development practices are generally working to prevent the most egregious issues from surfacing in the code in the first place.
We mentioned in our last audit report that we believe that this audit makes WPCD the most secure plugin of its kind. And arguable more secure than some SaaS management panels since you:
- Know that a security audit was done.
- Know WHEN the security audit was done.
- Know the results of the security audit.
- Can view the raw audit report.
- Know that any discovered issues were handled and
- Can view the full source-code to verify issues and related fixes.
If you have any questions, please send us a note using either our ticket system or the support email address shown at the very bottom of this page.
Was This Article Useful? Or do you have questions or comments about it (or our products & services)? We'd love to hear from you!
Automatic Notification Of New Articles
Sign up to get automatic notifications of new articles. This is a different list than our standard list - you only get new articles once a week (usually on Mondays). No other emails will be sent unless you sign up for our general list as well.
Follow us on Twitter! We post a lot of cool things there first. To keep up, click the "X" below!